VPN alternatives offer diverse ways to secure your data and bypass geo-blocks without relying on a traditional encrypted tunnel. We believe that while a virtual private network is powerful, it is not always the most efficient tool for every specific online task.
You might find that a proxy works better for simple site unblocking, or that Tor provides a deeper level of anonymity for sensitive research. In this guide, we explore the most effective alternatives to VPN technologies to help you build a custom privacy stack that fits your 2026 digital lifestyle perfectly.
Why look for VPN alternatives?
VPN alternatives are the best choice when you need specialized performance or targeted access without the heavy overhead of a full encrypted tunnel. While VPNs protect your device, standard tunnels can slow your 4K stream or trigger security alerts on sensitive banking systems.
Many users find that alternative connections offer a more nimble way to navigate the web in 2026. There are several key reasons to consider alternatives for your digital setup:
- Higher Streaming Speeds: Avoid the “encryption tax” that causes buffering in high-definition video.
- Granular Network Control: You gain more precise management over your data flow rather than securing the whole device.
- Lower Latency: Reduces the millisecond delays often found in multi-hop encrypted tunnels.
- Sensitive Site Access: Some banking systems block standard VPN IPs but allow specialized proxies or DNS shifts.
- No Software Bloat: You can secure your connection without a paid VPN or installing free software on every device.
- Selective Location Spoofing: You might only need to change your location for a single browser tab to access local news.
- Better Compatibility: Certain smart TVs and consoles work better with DNS-based alternatives to VPN connections.
By understanding these specific needs, you can choose a tool that effectively balances your protection and performance. Since we have explored why users seek different options, we can now look at specific VPN alternatives designed for individual privacy.
Best VPN alternatives for personal privacy
We just examined the core reasons for making a switch, so let’s explore VPN alternatives that offer the best protection for your personal identity. These alternatives focus on identity masking and targeted data streams to prevent tracking.
| Service | Best For | Pricing | Key Trade-off |
| Tor (The Onion Router) | Maximum anonymity for sensitive research | Free | Severe speed loss makes streaming 4K video nearly impossible. |
| Proxy Servers | Fast IP spoofing to bypass basic regional blocks | Paid / Free | Lacks data encryption; your ISP can still see your traffic content. |
| Private DNS | Protocol-level security and ad-blocking at the source | Free | Does not hide your real IP address from the websites you visit. |
| Browser Extensions | Light web surfing without slowing down other apps | Mostly Free | Only secures browser traffic; system-level apps remain fully exposed. |
Tor (The Onion Router)
Tor is a decentralized network that bounces your traffic through three volunteer nodes to make your digital origin nearly impossible to trace. This tool is the gold standard for alternatives to VPN when absolute anonymity is your primary goal.
You can browse sensitive topics without trusting a single company, as no single entity controls the entire path. The multi-layered encryption ensures that even if one node is compromised, your identity remains hidden.
- Pros: Ultimate anonymity, no central point of failure, free to use.
- Cons: Significantly slower speeds, some websites block Tor exit nodes.
Tor remains the top choice for whistleblowers and researchers who value privacy above all else.
Proxy servers

Proxy servers act as intermediaries between your device and the internet to hide your real IP address without encrypting your entire data load. This makes them excellent VPN alternatives for tasks like web scraping or bypassing basic regional filters.
We suggest using an anonymous proxy service to ensure your traffic remains hidden from the destination site. Proxies are generally faster than VPNs because they do not have the heavy encryption overhead.
- Pros: Very fast connection speeds, easy to set up, perfect for simple unblocking.
- Cons: No end-to-end data encryption, less security for sensitive logins.
Proxies are a great fit for users who need to change their location without losing speed.
Private DNS services
Private DNS services replace your ISP’s default servers to prevent them from logging which websites you visit while potentially speeding up your connection. These are subtle VPN replacements that improve privacy at the very foundation of your internet connection.
By using encrypted DNS, you stop “man-in-the-middle” attacks that redirect you to fake websites designed to steal your data. While a DNS change does not hide your IP from the websites you visit, it is a vital layer in a modern privacy strategy.
- Pros: Enhances basic privacy, protects against DNS hijacking, no app needed.
- Cons: Does not hide your IP address or encrypt the actual content of your traffic.
Private DNS is the perfect starting point for users looking for a faster, more secure baseline for their browsing.
Browser privacy extensions

Browser extensions provide a lightweight way to encrypt traffic only within your web browser, leaving other apps on your device to run at full speed. These are the most common solutions for casual users who only need to secure their web browsing.
We often recommend checking how to use a VPN in incognito mode to ensure your extensions stay active during your most private sessions. They are easy to toggle on and off, making them perfect for quick site access.
- Pros: Extremely easy to use, does not slow down background apps, often free.
- Cons: Only protects browser traffic, can be detected by some advanced sites.
Browser extensions are the ideal “one-click” solution for securing your daily web activity.
Securing your personal data is just the beginning; many VPN alternatives are also designed to maximize your streaming speeds.
Best VPN alternatives for streaming and speed
To help you find the fastest connection, we have compared the best VPN alternatives for your 2026 media needs. These solutions focus on raw speed for 4K video by removing the “encryption tax” found in standard tunnels.
| Service | Best For | Pricing | Key Trade-off |
| Smart DNS | Smart TVs & Consoles | Paid/Free | Provides zero data encryption or privacy. |
| Residential Proxy | Bypassing strict blocks | Paid | Can be much more expensive than a VPN. |
| Browser Proxy | Quick web unblocking | Mostly Free | Only works for traffic within a single browser. |
Smart DNS

Smart DNS has evolved from a niche technical workaround into a premier solution for global streaming access. This technology intercepts and redirects only the DNS queries that reveal your physical location, allowing you to bypass geo-blocks with zero speed loss.
You can enjoy international libraries on devices like Smart TVs and gaming consoles that rarely support traditional VPN apps. The viewing experience is identical to a local connection because your data packets are not encrypted or routed through a distant server.
- Pros: Fastest possible streaming speeds, works on almost every device, and has a very easy setup.
- Cons: No privacy protection or encryption, doesn’t hide your IP from other services.
Smart DNS remains a top-tier choice for entertainment lovers who want to centralize their global streaming access without lag.
Proxy vs VPN for streaming
Residential proxies have become a powerful alternative to VPNs for users trying to access platforms like Netflix or Hulu. Unlike standard datacenter IPs, these proxies use real home IP addresses, making them much harder for streaming services to detect and block.
While a VPN provides a secure tunnel, a high-quality residential proxy is often more reliable for maintaining access to high-demand content. You avoid the “VPN detected” errors that frequently interrupt your binge-watching sessions.
- Pros: Harder for streaming sites to block, excellent for 4K video, no encryption overhead.
- Cons: Can be more expensive than standard VPNs, and offers no security for sensitive browsing.
Proxies are a perfect fit for users who prioritize content availability and raw speed over background data security.
While streaming is a personal choice, businesses require alternatives that can handle massive data loads and securely support hundreds of remote employees.
Best VPN alternatives for business and enterprise security
After securing your personal data, you need VPN alternatives that handle high-definition media without the lag of full encryption. These alternatives provide a “never trust, always verify” model that is much safer than a single hardware tunnel.
| Service | Best For | Pricing | Key Trade-off |
| ZTNA | Granular app access | High | Requires complex, ongoing identity management. |
| SASE | Cloud-first security | High | High implementation costs and vendor lock-in. |
| SD-WAN | Multi-site connectivity | Varies | Lacks native user encryption; needs extra layers. |
Zero Trust Network Access (ZTNA)
ZTNA has moved from a complex IT concept to a powerhouse alternative to legacy VPNs for remote work security. This service is a perfect fit for modern companies because it grants access based on identity rather than location.
You can ensure that employees only see the specific applications they need, effectively hiding the rest of the network from potential threats. This “dark cloud” approach prevents hackers from moving between departments even if they manage to compromise a single device.
- Pros: Granular security controls prevent lateral movement by attackers and improve the user experience.
- Cons: Setup can be complex for small teams, and requires active management of user permissions.
ZTNA is a top-tier choice for security-conscious enterprises that want to move away from the “all-access” risks of traditional tunnels.
Secure Access Service Edge (SASE)
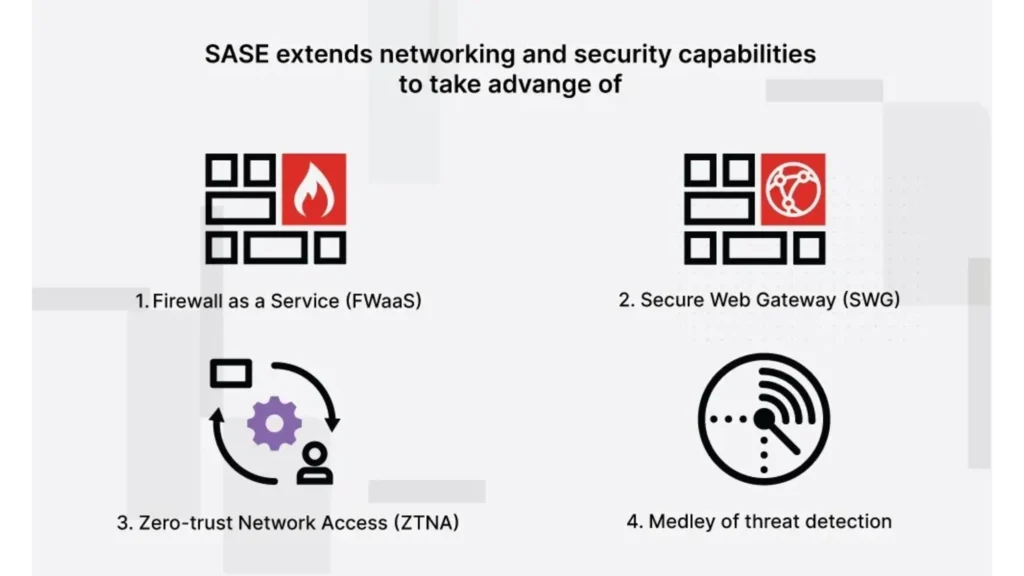
SASE combines network security and wide-area networking into a single cloud-native service. It represents the future of VPN alternatives by moving security to the “edge” closest to the user, reducing the latency caused by backhauling traffic to a central office.
Employees get a faster, more reliable connection to company cloud apps like Salesforce or Slack, regardless of where they are working. The security is integrated directly into the network fabric, ensuring protection is always “on.”
- Pros: Simplifies network management, reduces latency for global teams, and scales easily.
- Cons: High implementation costs, can create vendor lock-in for large organizations.
SASE remains the best solution for large-scale businesses that require a unified security and networking strategy.
Software-Defined WAN (SD-WAN)

SD-WAN is a software-based solution that optimizes connectivity between office locations and data centers. While not a direct encryption tool, it is an essential alternative to VPNs for managing large-scale network performance and stability.
You can mix fiber, 5G, and broadband connections to ensure your business applications always have the fastest available path. This flexibility prevents network downtime and ensures that video calls and large file transfers remain smooth during peak hours.
- Pros: Maximizes bandwidth efficiency, improves application performance, easy to manage remotely.
- Cons: Does not provide end-to-end user encryption on its own, requires additional security layers.
SD-WAN is a top-tier choice for businesses with multiple locations that need to centralize their network management.
Understanding these technical distinctions helps you know exactly when to stick with your current setup and when to switch.
VPN vs alternatives: What’s the difference?
The main difference between a VPN and VPN alternatives is the scope of data protection and the overall impact on your 2026 connection speed. While we define a VPN as a general-purpose security tool that secures your entire device, these alternatives are specialized tools for specific tasks.
Some users worry that free VPNs can really offer unlimited data without a catch, which is why specialized alternatives to VPN connections are often more transparent. To help you decide between a full shield and a surgical tool, we have compared Standard VPN technology with every top alternative below.
| Solution | Primary Function | Encryption Level | Best 2026 Use Case |
| Standard VPN | Full device tunnel | High (AES-256) | Total daily privacy |
| Tor | Multi-layer routing | Extreme | Absolute anonymity |
| Proxy Servers | IP masking only | None / Low | Content unblocking |
| Private DNS | Address resolution | None | Stopping ISP tracking |
| Extensions | Browser-only shield | High (In-browser) | Quick web tasks |
| ZTNA | App-level access | High | Secure remote work |
| SASE | Edge security | High | Cloud enterprises |
| SD-WAN | Traffic routing | Varies | Multi-site networking |
Understanding these technical distinctions helps you know exactly when to stick with your current setup and when to switch to one of these technologies. While alternative connections offer incredible speed, they often lack the “all-in-one” safety of a traditional provider like TurisVPN. None of these provides the exact same package, but they perform their roles better than a jack-of-all-trades tool would.
Having compared the features, we can now define exactly when you should use a VPN instead of these specialized tools.
When should you use a VPN instead of alternatives?
You should use a VPN instead of VPN alternatives when you are on public Wi-Fi or need total data privacy across all applications on your device. While we love the speed of proxies, they do not protect your banking app or your email client from local hackers.
Many users naturally wonder if a VPN can be hacked by these intruders, but a robust, encrypted tunnel remains your strongest defense. We recommend staying with a VPN for:
- Online banking and sensitive financial transactions.
- Protecting your data while using airport or coffee shop Wi-Fi.
- Avoiding ISP throttling across all your internet activities.
- Ensuring that your metadata is completely hidden from advertisers.
Choosing the right tool ensures you remain safe without sacrificing the speed you need for your daily tasks.
Bottom Line
VPN alternatives are vital tools in 2026 for anyone looking to optimize their digital privacy, streaming performance, and network security. Whether you are a business securing remote workers or a traveler trying to watch home content, there is a tool designed for your exact problem.
At TurisVPN, we encourage you to experiment with these alternatives to find the perfect balance for your needs. If you ever feel that these alternatives are too complex, a reliable VPN remains the most user-friendly way to stay safe online with just one click.
FAQs
1. Are VPN alternatives safe?
These solutions are safe as long as you choose reputable providers and understand each technology’s limits. A proxy server hides your IP address but does not encrypt your data, making it safe for streaming but risky for banking. Always verify the privacy policy of any tool you use to ensure they do not log your activity.
2. Is Tor better than a VPN?
Tor is better than a VPN for absolute anonymity because it uses a decentralized network, but it is much slower. Most users find VPN alternatives like Tor too frustrating for daily use or video streaming. If you are a journalist in a high-risk area, Tor is the right choice; for everyone else, a VPN is usually better.
3. Do VPN alternatives protect your data?
Some VPN alternatives protect your data with encryption, while others only change your visible location. ZTNA and Tor offer high levels of data protection, but Smart DNS and basic proxies do not. You must check the specific features of the alternatives you are considering to ensure they meet your security standards.
4. What is the best alternative to a VPN?
For most people, an anonymous proxy or a privacy-focused browser extension is the top choice. These alternatives to VPNs offer a good balance of speed and basic IP masking. For businesses, ZTNA is currently considered the gold standard for modern network security.